THE BETRAYAL
OF THE NETWORK’S FREE ORBIT
Internet, Utopia, and Freedom: The Brief Escape from Capitalism
October 29, 1969. UCLA computer lab. Charley Kline types the first message in the history of the network. Destination: the Stanford Research Institute, 350 miles north. The message was LOGIN. The system crashed at the second letter. Only two characters made it through: LO.
In September 2023, Microsoft signed a deal to restart Three Mile Island — the site of the worst civilian nuclear accident in American history, shuttered for decades — not to heat homes. To power Azure’s servers. To run language models that produce text, images, decisions on demand, at any hour, for anyone with a subscription.
Between these two images lies half a century. In between is something that doesn’t have an easy name: not a defeat, not a betrayal, not an inevitability. Something rarer and more final.
Internet network power: The Rule That Never Changes
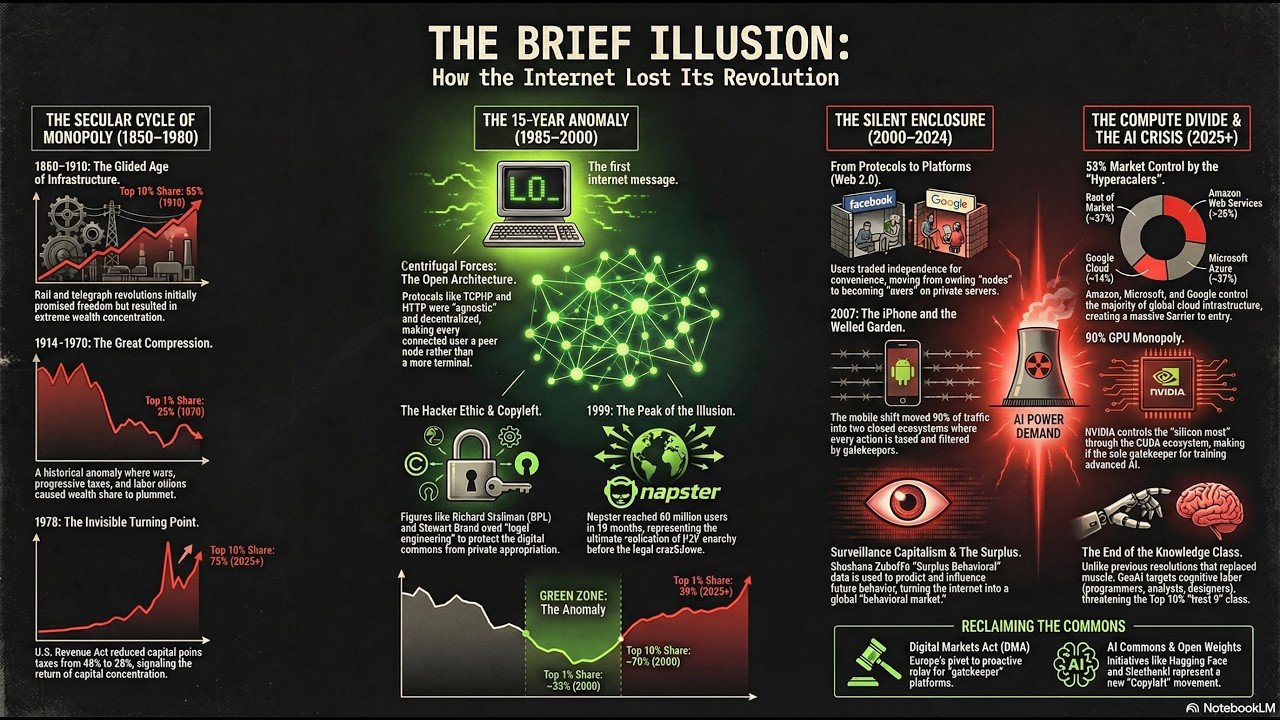
The history of technological revolutions is always the same story. Whoever controls the infrastructure controls everything else.
Steam democratized nothing — it concentrated capital in the hands of those who owned the railways. Cornelius Vanderbilt understood before most that it didn’t matter who used the tracks. What mattered was who owned them. Electricity repeated the script: the Gilded Age of Rockefeller and Carnegie wasn’t an accident of industrial capitalism — it was its logic applied consistently. Computing in the 1960s and 1970s confirmed the rule. The mainframe was physically massive, economically inaccessible, exclusively owned by IBM or the U.S. federal government. Access to computation was access to power, and access to computation was reserved for those who already had power.
“Every technological revolution in history has functioned as a centripetal force — pulling power and capital toward the center, not dispersing them. The rule had held for two hundred years.”
Then, between 1985 and 2000, the rule broke.
The Signal Nobody Read
But first — eleven years before the open internet reached critical mass — a technical clause in a budget law changed the direction of the curve. On November 6, 1978, the U.S. Congress passed the Revenue Act. The maximum capital gains tax rate fell from 49% to 28%. Sixteen percentage points. The starting gun for private capital toward high-risk, high-return markets — toward exactly the nascent sectors that, a decade later, would fund Silicon Valley.
This isn’t 1979 Thatcher. It isn’t 1980 Reagan. Those events come after, and they get cited because they’re visible, nameable, attributable to a face. 1978 is a technical sentence in a budget law that nobody outside Congress reads. But it’s the moment the curve begins inverting its direction. Before there was an internet. Before there was Silicon Valley as we know it.
This date matters because it inverts the conventional narrative: the internet didn’t emerge at the beginning of a new era of open possibility. It emerged as centrifugal resistance inside a trajectory that was already adverse. What follows is the history of that resistance — how long it lasted, what produced it, how it closed.
Internet old dream: The Historical Anomaly
Norbert Wiener, the father of cybernetics, built in the 1940s a theory of systems that was, in essence, a political theory disguised as mathematics. Its core principle: complex systems self-regulate through feedback that circulates freely between nodes. No central control required. No mandatory hierarchy. Only information flowing — and systems learning from it.
TCP/IP, the protocol that still holds up the internet today, was cybernetics applied to infrastructure. Intelligence lived at the edges — in users’ computers. The core infrastructure moved packets without knowing what they contained, without class distinctions, without tolls. Anyone with a modem and a phone line could become a node structurally equivalent to the Pentagon. Not technically identical — structurally equivalent.
But TCP/IP didn’t emerge from nowhere. Standard histories decompose the genesis of the internet into separate elements — the military lab, the university, the California garage, the hacker collective — as though each were an independent cause that adds up to the others. This framework betrays the phenomenon. They weren’t parallel causes: they were frequencies amplifying each other, constructive interference on a historical scale.
The initial perturbation was the Second World War. Los Alamos, Bletchley Park, the MIT Radiation Laboratory — these places shared a structural feature: radical peer-to-peer sharing of information was the only way to survive. It wasn’t ethics. It was survival engineering. When the war ended, that practice migrated into the universities and laboratories that would build, twenty years later, the first digital networks. The culture of openness didn’t precede the network as an ideology. It preceded it as a conditioned reflex of wartime collaboration.
The second amplification system is the most counterintuitive: the convergence of the European academic tradition and the California counterculture — two traditions that never spoke to each other, producing the same structural output. Tim Berners-Lee didn’t patent HTTP or HTML. He gave them to the world in 1991 — a conditioned reflex of a culture that considered knowledge a public good by definition. Stewart Brand founded the Whole Earth Catalog in 1968 as a tool of radical autonomy: a distributed system of shared knowledge where value increased with circulation rather than restriction. In 1984, Brand said it with the sharp clarity of someone who truly knows a system: “Information wants to be free. Information also wants to be expensive.” It wasn’t rhetorical ambiguity. It was a diagnosis of structural tension — and a prophecy everyone remembered wrong by quoting only the first half.
On February 8, 1996, John Perry Barlow was in Davos. That night, in his hotel room, he wrote the Declaration of the Independence of Cyberspace: “Governments of the Industrial World, you weary giants of flesh and steel: I come from Cyberspace, the new home of Mind. On behalf of the future, I ask you to leave us alone.”
It wasn’t romanticism. It was physics. For the first time in the history of technological networks, infrastructure was designed to resist concentration.

Napster, in 1999, was the rehearsal. Eighty million users in eighteen months — the largest music library ever built, constructed without a cent of investment in content. It wasn’t piracy. It was the technical materialization of the distributed anarchy Wiener had theorized. Wikipedia, Creative Commons, BitTorrent: the self-reinforcing system had produced institutions that institutionalized itself.
Then came the revelation. On February 12, 2001, a Ninth Circuit Court of Appeals ruling forced Napster to disable copyright-infringing sharing. To comply, Napster had to build a central server. A point that could be turned off.
But the defeat exposed something deeper than a technical vulnerability. The boundary between the protocol layer — invulnerable to technical censorship, because TCP/IP has no center to target — and the application layer — vulnerable to concentrated legal pressure — was the line through which capital would recover control. The protocol couldn’t be attacked. So the ecosystem around the protocol was attacked instead. The Digital Millennium Copyright Act, already in force since 1998, was the instrument used to pressure internet providers into removing content on simple notification. Not piracy enforcement — ecosystem management.
There is a third level, more structural than both. The communities of practice that had generated the internet had built open infrastructure without building the political institutions capable of defending it. Capital understood appropriation mechanisms far better than hacker communities understood legal mechanisms. The locks were built before the network reached critical mass: software patents, contributory infringement doctrine, DMCA notice-and-takedown. The keys were already in the hands of the recording industry, the film industry, the U.S. patent system. Napster’s defeat didn’t mark the end of peer-to-peer. It marked the moment the boundary of the resonance field became visible.
The Architecture of Capture
Michel Foucault analyzed Bentham’s Panopticon as an architecture of invisible power: the watched person doesn’t know when they’re being observed, but knows they could be observed at any time. The result is self-discipline. You don’t need guards if the prisoner watches themselves.
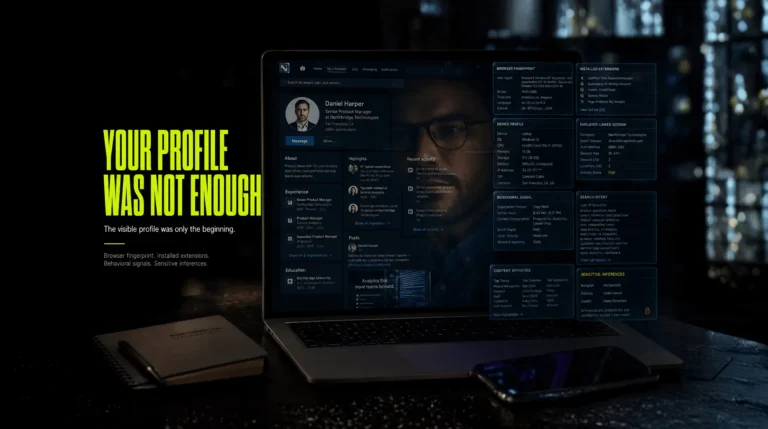
But there’s a second Foucauldian level, more precise and more unsettling. Mature power doesn’t operate through prohibition. It operates through the production of subjectivity. Algorithms don’t forbid: they produce the kind of user who desires what platforms want them to desire. They don’t stop you from thinking differently. They build you so that thinking differently doesn’t even occur to you.
B.F. Skinner built the mechanism in a lab decades earlier. Variable-ratio reinforcement — rewards arriving unpredictably — produces behavioral addiction stronger than any constant reinforcement. It’s the slot machine principle. The infinite feed is Skinner engineered into the interface. You don’t know when the like will arrive, the comment that hits you, the content that makes you feel seen. Variable reinforcement turns the thumb gesture into a loop with no natural exit. Skinner was honest in his brutality: he wanted to eliminate the very notion of free will as an explanatory category for behavior. Platforms took his toolkit, wrapped it in colorful icons and sixty-page terms of service.
Then Cass Sunstein arrived — and provided the justification.
Nudge, written with Richard Thaler in 2008, introduced libertarian paternalism: institutions should design decision environments to steer choices toward desirable outcomes, while formally preserving freedom of choice. You don’t force. You don’t prohibit. You architect the environment so the “right” choice is the easiest one. Sunstein was thinking about public retirement programs. Designers at Facebook, Instagram, and TikTok were thinking about average session time. Same framework. Opposite goals.
“Sunstein is Skinner in a suit, sitting at the White House table. The difference is that Skinner didn’t pretend to preserve freedom. Dark patterns, default opt-ins, calibrated notifications: they’re all nudges. Choice architecture that chooses for you.”
In Republic.com, published in 2001, Sunstein had already described echo chambers with precision. He had the diagnosis. He didn’t — or didn’t want to have — the consequence: that the same logic produces behavioral capture, and that both are functional to a system that needs attention concentrated inside proprietary silos.
The Enclosure of Internet
The dot-com crash of 2000 wasn’t the end of the digital utopia. It was the moment capitalism figured out how to absorb it. Like the enclosures of English common land between the 16th and 19th centuries — which transformed shared resources into private property not through violence but through legal instruments, incrementally, with apparent inevitability — Web 2.0 fenced the open infrastructure of the network into closed ecosystems. The decisive difference: this enclosure happened largely without users noticing. Often with their enthusiastic consent.
In Web 1.0, every user could be a peer node on open protocols. Email ran on SMTP, POP3, IMAP — protocols no one owned that anyone could implement. In Web 2.0, we became terminal users uploading data to centralized servers owned by private companies. Not nodes: terminals. Not publishing: uploading. Not communicating: feeding someone else’s database. The difference wasn’t visible in the interface. It was invisible, infrastructural, decisive.
Google appropriated the semantic layer of the network. Not the data — that stayed on everyone’s servers. Not the protocols — those stayed open. But meaning: the capacity to determine which pages were relevant for which query, and therefore which voices could be heard at what price of attention. Facebook made the definitive synthesis: social graph, content, identity, private communications — all inside one closed system, monetizable through behavioral advertising. The exit cost wasn’t technical but relational. Facebook owned the context, not the content. And context can’t be ported. The iPhone’s App Store — 30% tax, editorial control over every application — completed the enclosure at the level of the physical device. Today over 90% of global internet traffic flows through two closed mobile ecosystems.
Wiener’s metaphor had inverted: the center was intelligent again, and the margins had become terminals again.
Five Generations, One Amnesia
Walter Ong showed that communication technologies don’t merely transport content: they restructure the cognitive categories through which content is thinkable. The printing press made possible forms of individual cognition that the manuscript couldn’t support. Platforms are doing the same thing — in the opposite direction.
Five generations have passed through the closing of the window with progressively different cognitive outcomes.
The Founders (1969–1985) invented the network. They know what it could be because they built it. The Builders (1985–2000) inhabited it. They believed in it for idealism and material interest simultaneously — Napster was proof the dream was workable. The Betrayers (2000–2010) built it while closing it, without knowing they were betraying anything. They had already grown up inside a different cognitive environment. The open web was a story old people told. The Heirs (2010–2020) don’t know it ever existed. The platform is the world — not one of the possible worlds. The fifth generation, today, inhabits an environment where AI produces the world: there is no longer a perceptible difference between infrastructure and reality.
It wasn’t a betrayal. It was something harder to name: the natural product of a generation that inherited the infrastructure without inheriting the vision that had built it. Infrastructures are transmitted. The visions that generated them are not — at least not automatically. And each subsequent generation inherited a further reduced cognitive environment.
You cannot explain the difference between an open protocol and a closed API to someone whose entire experience of “the network” has been mediated by proprietary interfaces. Not because they lack intelligence. Because they lack the experiential categories to make that difference felt, not merely understood. The platform has replaced the categories through which the outside would be thinkable. You don’t only select what you think. You reduce the range of what is thinkable.
The Wall You Don’t See Because It’s Everywhere
The subjectivity produced by platforms needed a body. The body was the cloud.
Starting in 2010, the entire world economy runs physically inside the data centers of three companies: Amazon Web Services, Microsoft Azure, Google Cloud. If AWS shuts down at 3 a.m., half the internet disappears. That’s not hyperbole — it’s happened. “Independent nodes” are virtual machines running on someone else’s hardware, in someone else’s buildings, in jurisdictions negotiated with someone else’s state. Wiener’s decentralization became an administrative fiction.
Combined share of the cloud market held by AWS, Azure, and Google Cloud
Share of advanced GPU market controlled by NVIDIA for AI training
Estimated compute cost of training a frontier model before data and labor
STRUCTURAL CONCENTRATION · CLOUD · COMPUTE · ENERGY
Three companies control over 63% of a cloud market worth $400 billion per year. NVIDIA controls 80–90% of the advanced GPU market for AI training. The total compute cost of training a frontier model is estimated between $50 and $100 million — before data, infrastructure, and human capital. Only seven or eight organizations in the world have access to this scale of resources.
Three Mile Island restarted to power Microsoft’s servers is not an anecdote. It’s the exact symbol of this concentration. According to Goldman Sachs estimates, by 2030 AI data centers could consume up to 3–4% of global electricity. This energy dependency transforms the Compute Divide into a matter of sovereign deterrence: only nations with stable, industrial-scale access to cheap energy can host competitive AI infrastructure. The Compute Divide has become a geopolitical weapon.
Every previous technological revolution replaced muscles. Steam, electricity, automation devalued physical labor and rewarded cognitive labor. The third industrial revolution — computing, software, the internet — created a new aristocracy of work: knowledge workers. Between 1970 and 2000, the wealth share of the Top 10% rose from 60% to 70%. Ten points in thirty years. It looked like proof that technology could distribute prosperity, if not downward then at least broadly upward.
The AI revolution is changing this dynamic in a structurally novel way. Previous revolutions automated routine cognition and created demand for non-routine cognition. This one automates non-routine cognition of middle complexity — exactly what filled offices and built careers for thirty years. The mid-level programmer. The translator. The junior consultant. The data analyst. The standard copywriter.
The Top 1% — those who own servers, patents, cloud networks, compute — captures the largest share of AI productivity gains. The Top 10% — the professional class that believed it had won the bet of the third industrial revolution — now finds itself where blue-collar workers were in the 1980s: not poor, not excluded, simply less necessary. Piketty’s formula — r > g, the rate of return on capital exceeding the rate of economic growth — re-sharpens in a new form: the returns from cognitive automation won’t be distributed to the workers replaced. They will go to the owners of the infrastructure that makes that automation possible.
“Previous revolutions replaced muscles and created cognitive work. This one automates average cognition and creates rent for those who own compute. The class that thought it was safe because it ‘thinks’ discovered that replicable thinking is no longer a competitive advantage.”
Old Internet and Questions That Remains
The counter-utopia if Internet exist. In 2021, analysis of Web3’s “decentralized” blockchain networks revealed that most nodes ran physically on Amazon Web Services and Google Cloud. The dream of autonomy paying rent to its feudal lord. Digital anarchy hosted on the infrastructure of its enemy, billed by the hour. It doesn’t defeat you. It includes you. It runs you on its servers while you declare independence from the server.
The Fediverse — Mastodon, Bluesky, PeerTube — is more honest in its premises: it promises communicative decentralization rather than economic decentralization, using open protocols like ActivityPub as a modern SMTP for social media. But it faces the same structural problem: freedom requires friction, and the majority of users prefer comfortable chains to difficult liberty. Small surges after every Big Tech scandal, followed by the difficulty of retaining critical mass.
There are precise answers — not vague gestures toward “digital sovereignty.” Coercive interoperability: legally mandated data portability and protocol openness for dominant platforms, making exit costs technical rather than relational. Public investment in open cloud infrastructure at the scale of the CHIPS and Science Act ($52 billion) — because the lesson of Europe’s failed Gaia-X project is that you cannot build infrastructure through public-private partnership where the private sector sets the terms. An AI Commons License: permits commercial use of models but prohibits proprietary enclosure of training data produced by user contributions — copyleft logic applied to machine learning.
Wiener warned that feedback systems could be captured. Brand said information also wants to be expensive. McLuhan told us it was the medium, not the message. Foucault described the prison built from the inside. Skinner built the slot machine. Sunstein gave it a presentable justification. The pieces were on the table. We walked past them one by one without stopping.
The fifteen years of the open internet were not nothing. They were empirical proof that the alternative was real. Wiener’s dream — information flowing freely between peers, complex systems self-correcting through open feedback — has not been cancelled. It has been temporarily suspended.
And Wiener’s question, asked in 1950 before the internet existed, before the personal computer existed, remains standing — more urgent than it has ever been: We are building machines that make decisions faster than we can follow them. The question is not whether this is inevitable. The question is who decides the rules by which the machines make their decisions.
The centrifugal force wasn’t defeated from the outside. It was seduced from within, piece by piece, convenience by convenience, nudge by nudge. The historical rule wasn’t broken by technology. It was restored by the very technology that, for fifteen years, promised to break it forever.
DIDN’T DEFEAT YOU.
IT MADE YOU
CENTRIPETAL.